
As vehicles evolve into software-defined platforms…
…cyber security is no longer a bolt-on feature — it’s a foundational requirement. But the real question is whether it can be modular, upgradable, and user-controllable. This chapter explores the future of vehicle security as a replaceable subsystem, akin to how stereos once slotted into DIN-standard dashboards. We examine the technical feasibility, regulatory implications, and strategic ownership of these systems — and whether automakers can be trusted to deliver closed, proprietary security in a world that increasingly demands transparency.
The closed standards club: Who shapes vehicle cyber security?
Much like the IETF (Internet Engineering Task Force) standardised internet protocols to enable secure, interoperable networks, AUTOSAR (AUTomotive Open System ARchitecture) plays a similar role in the automotive domain — defining open software architectures that allow ECUs, cloud services, and embedded systems to work across brands and suppliers. The comparison is useful, but imperfect.
While the IETF was built on openness and academic collaboration, it wasn’t immune to dysfunction. Progress was often slow, and large corporations could flood working groups with delegates to sway consensus by volume rather than merit. AUTOSAR, by contrast, is more vertically integrated and industry-driven, with core members like BMW, Toyota, Ford, Bosch, and Continental shaping the roadmap. It delivers technical consistency, but with limited transparency.
Unlike the IETF, AUTOSAR offers few formal pathways for independent researchers, user communities, or public-interest advocates to influence its direction. The architecture of vehicle cybersecurity is being defined largely behind closed doors — by OEMs, Tier-1 suppliers, and select industry partners. What remains unclear is how individual users, fleet operators, or grassroots technologists can formally shape these standards, despite being the ones most exposed to their consequences.
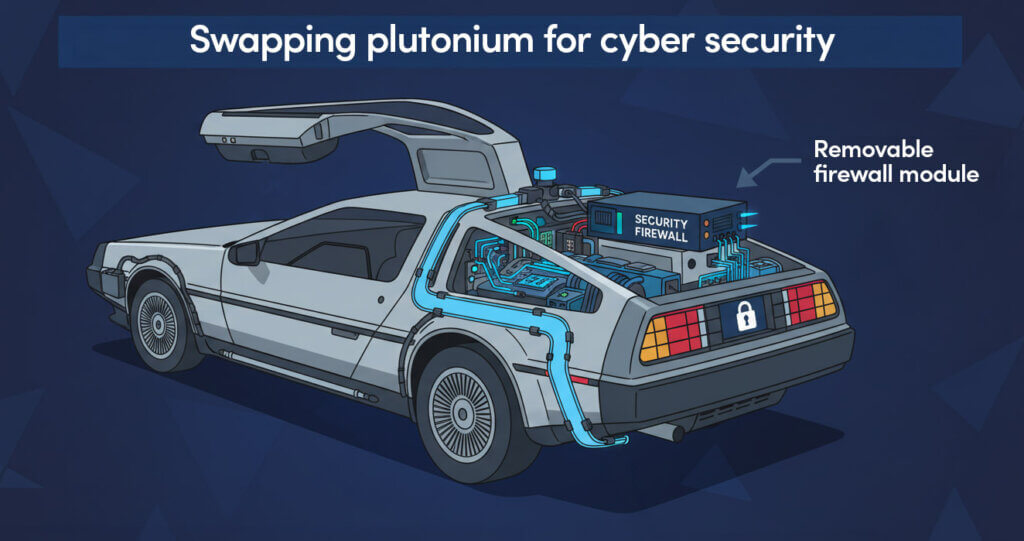
Modular security: From monoliths to replaceable defences
Traditional vehicle electronics were static and vendor-controlled. ECUs were hardwired, firmware was fixed, and cybersecurity — if present — was deeply embedded. But that architecture is being dismantled.
Today’s vehicles feature:
- Zonal architectures with centralised compute
- Ethernet-based communication with switch-level intelligence
- OTA pipelines and cloud-integrated diagnostics
- Containerised services running on Adaptive AUTOSAR platforms
This opens the door to modular cybersecurity subsystems — discrete components that can be upgraded independently of the vehicle’s core hardware. Examples include:
- Plug-in IDS modules that monitor zonal traffic
- Replaceable firewalls that filter external telemetry
- Consumer-accessible telemetry monitors
- Endpoint protection agents that can be updated or swapped like apps
AUTOSAR’s evolving roadmap supports this shift. Recent releases have introduced concepts like RemotePersistency for flexible data management, Vehicle Data Protocols for remote control and diagnostics, and Safe APIs for secure access to hardware accelerators — all designed to support distributed, cloud-aware security architectures.
Backend resilience: The new cyber security frontier
As highlighted in Part 2, backend systems have become the primary target. In 2024, more than half of automotive cyberattacks originated in cloud platforms — not the vehicle itself. The backend is now the perimeter. Once compromised, attackers can push malicious OTA updates, extract telemetry and user data, trigger remote immobilisation, and manipulate the behaviour of entire fleets.
To counter this, future protective controls must go beyond perimeter defence:
- Federated backend architecture: Segment cloud services by geography, function, or fleet type to contain breaches
- Policy-aware OTA gatekeeping: Require multi-layered validation and rollback triggers for critical updates
- Backend behaviour monitoring: Detect anomalous API calls and unauthorised data flows
- Decentralised trust anchors: Use hardware-based keys and multi-party attestation to prevent unilateral backend control
These measures shift backend security from passive infrastructure to active, policy-enforced resilience.
Island mode: Full telemetry isolation as a failsafe
Vehicles should support a telemetry isolation mode – a state where cloud connectivity is suspended, but core functionality remains intact. This “island mode” could be triggered manually by the user, automatically by anomaly detection, or enforced by policy in high-risk environments.
Key features:
- OTA updates paused
- Telemetry uploads blocked or sandboxed
- Remote commands disabled
- Local fallback logic activated
This concept aligns with AUTOSAR’s push toward RemotePersistency and Vehicle Data Protocols, enabling vehicles to operate securely even when disconnected from backend services.
Data governance: A GDPR for vehicle telemetry
LAs vehicles collect increasing volumes of data — location, driving behaviour, biometric inputs — there’s a growing need for a telemetry governance framework. A GDPR-style model would include:
- Disclosure: OEMs must inform users what data is collected, where it’s stored, and for how long
- Consent: Users must be able to opt in or out of specific telemetry categories
- Access: Users should be able to view, export, and delete their data
- Auditability: Third-party verification of data handling practices
AUTOSAR’s recent emphasis on data lifecycle management and cloud-integrated diagnostics provides the technical foundation. What’s missing is enforceable policy and consumer-facing transparency.
Security is not a subscription
Traditional vehicle electronics were static and vendor-controlled. ECUs were hardwired, firmware was fixed, and cybersecurity — if present — was dAs modular security becomes feasible, a troubling possibility emerges: OEMs may treat it like a feature — and charge for it. We’ve already seen this with heated seats and remote start. Cybersecurity must not follow the same path.
Imagine:
- Firewall updates gated behind a monthly fee
- IDS telemetry locked in a premium tier
- OTA patching throttled unless you upgrade to “CyberSecure+”
This isn’t hypothetical — it’s structurally possible. And unless regulators or consumers push back, it may become normalised. Security should be a standard, not an optional feature. Auditable, not proprietary. Upgradable, not monetised.
Lessons from infotainment: Why OEMs can’t be trusted alone
OEMs spent years trying to build proprietary infotainment systems — and failed. Poor UX, limited app ecosystems, and lagging performance drove users to demand open standards. Today, most automakers are migrating to Android Automotive and Apple CarPlay — not by choice, but by necessity.
Cybersecurity is heading down the same path. Closed, opaque stacks may satisfy compliance, but they won’t earn trust. Without visibility, users can’t verify whether their data is protected — or exfiltrated.
Who should own vehicle security?
This is the strategic question. Should cybersecurity be:
- OEM-controlled: tightly integrated, but opaque and vendor-locked
- Third-party managed: modular, auditable, and user-configurable
- Consumer-empowered: with dashboards, alerts, and override capabilities
Each model has trade-offs. A hybrid approach may be the answer:
- OEMs provide baseline security and regulatory compliance
- Third parties offer modular enhancements
- Consumers gain visibility and limited control
This mirrors enterprise IT, where vendor security is complemented by user-level controls and independent monitoring.
Next frontier: Autonomous vehicles, aerial and ground drones and ETOL
As Electric Take-Off and Landing (ETOL) platforms and driverless cars scale beyond prototypes, the need for modular, replaceable security becomes urgent. These platforms:
- Rely on real-time telemetry and cloud orchestration
- Operate in mixed-regulation environments
- Carry passengers, cargo, and sensitive data
- Make autonomous decisions based on external inputs
AUTOSAR’s roadmap supports this evolution. Features like CANsec, Safe APIs, and Vehicle Data Protocols enable secure, modular integration across air and road platforms. However, the challenge remains: how to protect algorithmic intent, enforce telemetry boundaries, and maintain operational integrity — even in the face of partial compromise.
Strategic insight: Security as a service layer
The future of vehicle cybersecurity isn’t monolithic — it’s layered and service-oriented. Just as infotainment became an app ecosystem, security will become a modular stack:
- Hardware-level protections (MACsec, secure boot)
- Middleware services (AUTOSAR IDS, DPI)
- Application-level controls (firewalls, telemetry dashboards)
- Cloud orchestration (SOC integration, OTA governance)
And like any service layer, it must be auditable, replaceable, and user-aware.
What comes next?
In Part 5, we’ll shift from architecture and strategy to actionable guidance. Whether you’re a driver, fleet operator, regulator, or technologist, we’ll explore how modular cybersecurity can be tailored to your role — from consumer firewalls and telemetry dashboards to procurement checklists and policy levers. The goal: to turn awareness into agency, and passive endpoints into active defenders.
About Reliance Cyber
Reliance Cyber delivers world class cybersecurity services tailored to the unique needs of our customers. With extensive in-house expertise and advanced technology, we protect organisations across a wide range of sectors — from enterprise to government —against the most sophisticated threats, including those from nation-state actors. Our teams safeguard critical assets, people, data, and reputations, allowing customers to focus on their core business objectives with confidence.
Get in touch with our experts
+44 (0)845 519 2946
contact@reliancecyber.com

